Ever wondered how companies protect themselves from online crooks? Enter IP fraud scores. These nifty tools help businesses spot potential cybercriminals before they can do any damage.
Imagine IP fraud scores, as virtual security guards. They monitor individuals attempting to visit websites or conduct transactions online. By examining elements associated with an IP address they can detect activities. It’s akin, to having an watchdog safeguarding your online abode.
In the age, with dangers present at every turn the significance of IP fraud-scores is, on the rise. These scores are not limited to companies they also offer advantages to small businesses and individuals by providing an added level of security. Lets explore further why these scores hold importance in combating cybercrime.
Understanding IP Fraud Scores
IP fraud scores are akin, to internet address evaluations serving as a measure of an IP addresss reliability determined by its activities. These assessments consider factors such, as the origin of the IP, its age and recent online activities.
Businesses utilize these ratings to determine whether they should grant individuals access, to their website or authorize a purchase. A low rating could indicate that the IP address is suspicious whereas a high rating indicates that it is likely safe. It’s a method to distinguish between users and those who may pose a threat online.
The Evolution of Cybercrime
In the past cybercrime used to be straightforward. Hackers would send out emails or set up poorly designed fake websites. However things have changed significantly now. Cybercriminals have become more cunning employing technology to hide their actions and deceive experienced internet users.
The advancements, in technology have compelled the individuals to enhance their strategies well. This is where the concept of IP fraud-scores plays a role. These scores represent a set of resources designed to combat the cunning cybercriminals. As the malefactors become more adept it becomes imperative for our defenses to adapt and progress in parallel, with them.
Related this post :Walkie-Talkie Etiquette Tips for Clear and Effective Communication
How IP Fraud Scores Detect Suspicious Activity
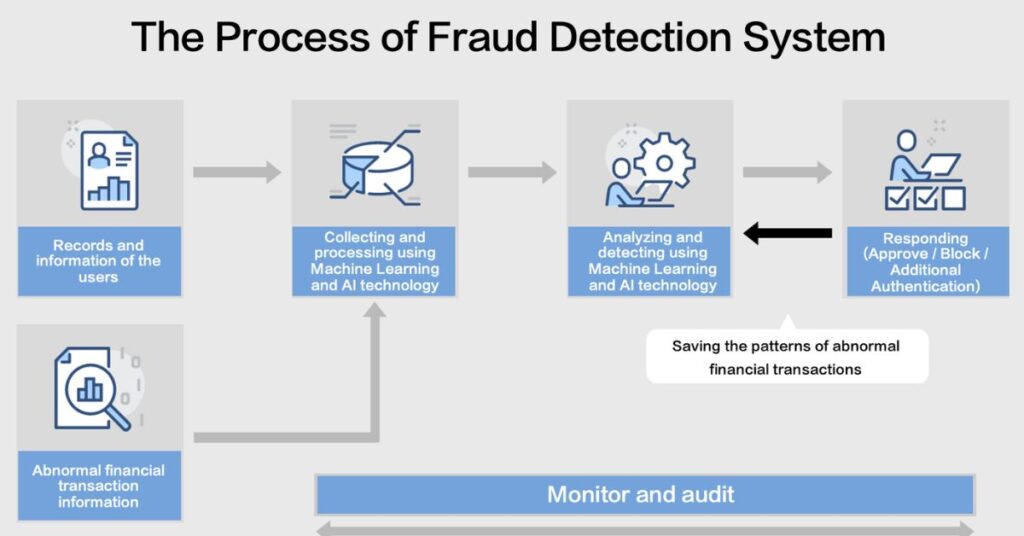
IP fraud-scores are like digital detectives. They look for clues that might suggest something’s not quite right. For example, they might notice if an IP address is trying to log in to lots of different accounts really fast. That’s a red flag that could mean someone’s trying to hack multiple users.
These scores also keep track of an IP’s history. If an address has been linked to fraud before, it’ll get a lower score. They even look at things like the time of day an IP is active or how it moves around the internet. All these little details help paint a picture of whether an IP is likely to be up to no good.
Integrating IP Fraud-Scores into Security Systems
Companies are weaving IP fraud scores into their digital defenses. It’s similar, to putting a layer of security on your door. These ratings complement firewalls and antivirus programs to build a defense against online dangers.
The integration process isn’t always smooth sailing, though. IT teams often face challenges when implementing these systems. But the payoff is worth it. A well-integrated IP fraud score system can catch bad actors before they even get a foot in the door.
Case Studies of IP Fraud Score Effectiveness
Let’s look at some real-world wins. A major online retailer slashed its fraud rates by 30% after adopting IP fraud-scores. That’s a lot of money saved and customer trust preserved.
Another example comes from a small e-commerce startup. They were drowning in fake orders until they started using IP fraud . Suddenly, their chargebacks dropped like a rock. It’s clear these scores pack a punch in the fight against cybercrime.
The Role of IP Fraud Scores in E-commerce
- Gatekeepers for online transactions
- Flag suspicious purchases in real-time
- Help maintain customer trust
- Reduce financial losses from fraud
E-commerce sites love IP fraud score. They work diligently like cashiers identifying bills before they reach the checkout. This results, in reduced chargebacks increased customer satisfaction and improved financial performance.
But it’s not just about stopping the bad guys. IP fraud-scores also help legit customers breeze through checkout. By quickly verifying trustworthy transactions, these scores keep the online shopping experience smooth and friction-free.
Enhancing User Authentication with IP Fraud Scores
IP fraud scores are beefing up login security too. They collaborate closely with passwords and two factor authentication to ensure the security of user accounts. It’s akin, to having a security guard who not verifies IDs but also watches out for any mischief makers.
- Adds an extra layer of account protection
- Helps identify account takeover attempts
- Reduces reliance on easily-guessed passwords
- Improves user experience for legitimate logins
This approach is changing how we think about online identity. We are moving away, from using passwords. Now taking into account the location of your login. This approach is more intelligent and comprehensive, in safeguarding against threats.
Challenges and Limitations of IP Fraud Scores
- VPNs and proxy servers may skew results
- Rapidly changing IP addresses complicate tracking
- Privacy concerns over data collection and usage
- Difficulty in keeping up with evolving fraud tactics
- Cost of implementation for smaller businesses
- Potential for overreliance on automated systems
- Geographical variations in IP reputation
- Limited effectiveness against sophisticated attackers
- Integration issues with existing security infrastructure
- Balancing security with user convenience
- Accuracy depends on quality and freshness of data
- May unfairly penalize users from high-risk regions
- Challenges in explaining decisions to affected users
- Potential for bias in scoring algorithms
Comparing IP Fraud Scores with Other Fraud Prevention Tools
Focusing solely on IP fraud-scores isn’t the strategy, in combating cybercrime. A variety of fraud prevention techniques are available including two factor authentication, biometric verification and the use of machine learning algorithms all contributing to thwarting criminals.
You know the interesting part is that IP fraud scores offer an advantage. They operate in time identifying risks before they have a chance to cause any harm. While other systems may only come into play once a user has already accessed the system IP fraud start working from the connection attempt. It’s similar, to having a bouncer who can detect trouble long before it approaches the entrance.
Also read this post : Evolution of CPUs: From Early Microprocessors to Powerhouses
Regulatory and Compliance Considerations
| Regulatory Considerations | Compliance Considerations |
| Set by government bodies | Often set by industry standards |
| Mandatory to follow | May be voluntary in some cases |
| Fines and legal penalties for non-compliance | Reputational damage for non-compliance |
| Focus on specific laws and regulations | Focus on broader best practices |
| Typically more rigid and prescriptive | Can be more flexible and adaptable |
| Often require external audits | May involve internal audits and self-assessment |
| Changes less frequently | Can evolve more rapidly with industry trends |
| Primarily about meeting legal requirements | Aims to improve overall security posture |
| Examples: GDPR, HIPAA | Examples: ISO standards, PCI DSS |
Future Trends in IP Fraud Scoring
The world of IP fraud scoring is evolving fast. We’re seeing smarter algorithms that can spot new tricks cybercriminals come up with. These systems are getting better at learning from each attempt, making them tougher to fool.
AI and machine learning are shaking things up too. They’re helping fraud detection systems work faster and more accurately. In the future, we might see real-time scoring that can stop attacks as they happen. It’s like having a digital superhero that gets stronger with each battle.
Best Practices for Maximizing IP Fraud Scores

To get the most out of IP fraud-scores, you’ve got to stay on your toes. Here are some tips:
- Keep your scoring system updated regularly
- Use multiple data sources to cross-check information
- Train your team to understand and act on score results
- Set clear thresholds for what counts as suspicious activity
Don’t forget to review and adjust your strategies often. What worked yesterday might not cut it tomorrow. It’s all about staying one step ahead of the bad guys.
- Monitor trends in your industry to spot new threats
- Collaborate with other businesses to share insights
- Test your system with simulated attacks
- Balance security with user experience to avoid false positives
Remember, the goal isn’t just to block threats. It’s to create a smooth, safe online experience for your legit users. With these practices, you’ll be well on your way to making the most of IP fraud scores.
Frequently Asked Question
What exactly is an IP fraud score?
It’s a number that rates how likely an IP address is to be involved in fraudulent activities.
How do IP fraud scores work?
They analyze various factors like location, browsing patterns, and historical data to assess risk.
Can IP fraud scores prevent all cybercrimes?
No, they’re just one tool in cybersecurity. They help, but aren’t foolproof.
Are high IP fraud scores always accurate?
Not always. They’re a strong indicator, but false positives can happen.
How often are IP fraud scores updated?
It varies, but most systems update scores in real-time or very frequently.
Conclusion
In the end, IP fraud scores aren’t just some techie jargon – they’re your digital bodyguards in the wild west of the internet. They’re working 24/7, spotting the bad apples before they can take a bite out of your online security. And let’s face it, in today’s world where cyber threats are as common as cat videos, we need all the help we can get.
But here’s the kicker: IP fraud-scores aren’t perfect. They’re more like a really good guess than a crystal ball. That’s why smart businesses don’t just rely on these scores alone. They use them as part of a bigger cybersecurity strategy, kind of like how you don’t just lock your front door – you also keep an eye out for suspicious activity in your neighborhood.